
The Joint Technology Committee (JTC) of COSCA, NCSC, CITOC, and NACM could never have known how predictive its Cybersecurity Basics for Courts report was when it published the work in December 2019.
A few months after release—when the unprecedented pandemic forced US courts to turn to technology to keep their doors open with remote and hybrid setups—that report began to read like a prophesy. In the early days of COVID-driven hearings, those working within the justice system quickly came to understand how critical cybersecurity is for courts employing any type of digital technology.
Today, as technology becomes increasingly accepted as part of daily court processes, court jurisdictions are paying heed to the JTC’s 2019 declaration that “every court will almost certainly face a cybersecurity incident including data breach or cyberattack.” After all, it has emerged in recent times that the US Federal Courts can be hacked, and Georgia’s court office files can be infiltrated by a ransomware attack.
Despite these incidents, technology will continue to be the future of modern justice. To ensure the digital court record is always both secure and accessible, here are some best practices for how courts can mitigate cybersecurity risks with For The Record.
Most courts are used to protecting text files and email correspondence on servers. But keeping digital court files under a physical lock and key is a traditional approach to a new-era issue.
Servers—even with best-practice network defenses—are vulnerable to other external threats. On-premises storage remains susceptible to the elements or damage, with limited back-up options available should an issue arise.
For example, in New Orleans, courthouses were flooded as waters rose during Hurricane Katrina, leaving records unusable. In 2019, wildfires threatened courthouses in California; while in 2020, the records stored in the courthouses of Nashville, Oakland, and Portland were at risk when fires and damage occurred during protests.
In today’s environment, the best safeguard against hackers, cybercrime, natural disasters, and other human interference is to store digital court records in the cloud—but there must be extra protection too.
Those files must always be protected by multiple layers of defense, secured with beyond-reproach encryption, and reinforced with anti-fraud tracking. That is where specialized justice technology becomes essential.
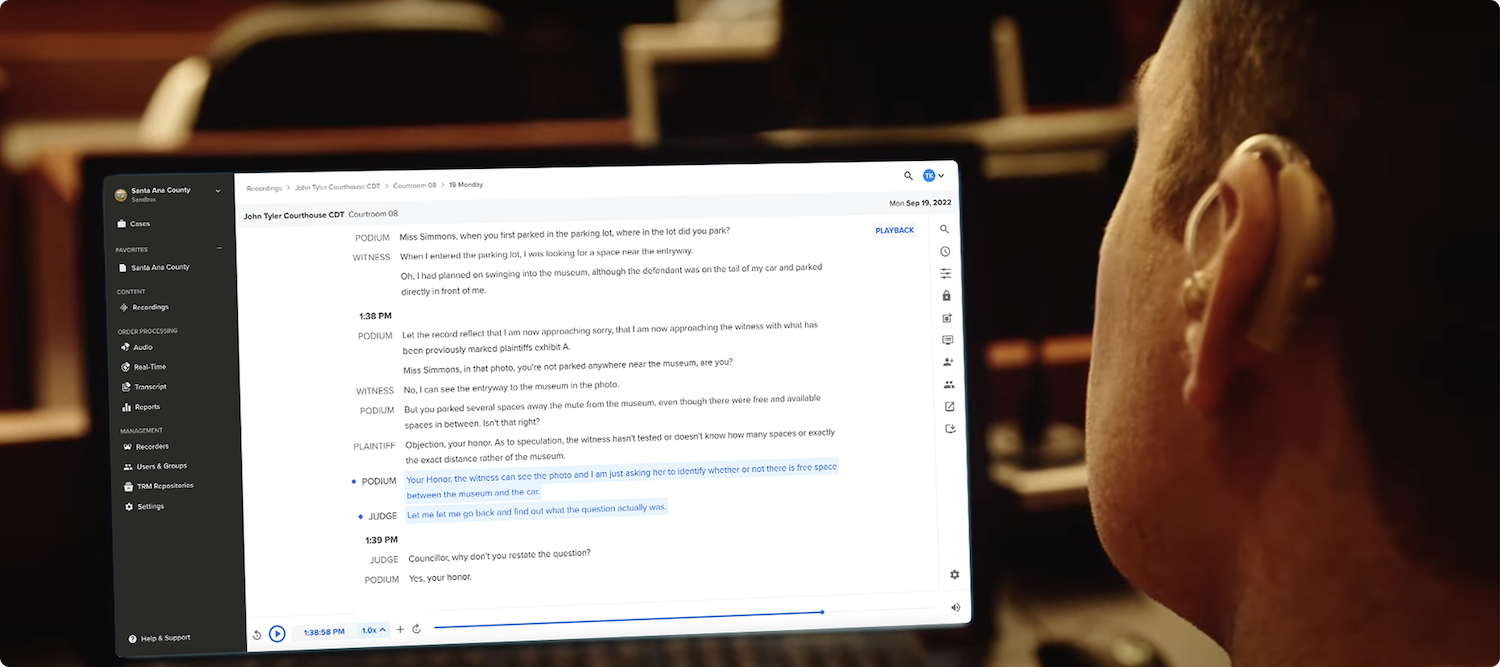
For The Record has a proprietary platform—FTR Justice Cloud—that stores the digital court record in the cloud, to then be accessed by judges, clerks, attorneys, parties, etc. Audio recordings of proceedings are crucial for public policy purposes, trial strategies, and judicial decision-making processes. Additionally, digitally stored audio can better comply with a jurisdiction’s retention policy for appeals.
Court data is stored inside a private tenancy, which means no one else can access the data unless the court themselves grants access. The court record is then accessible to those with a password and the right permissions, with approved users able to listen to and view the court record at any time, from any device.
Data security is paramount, too. To strengthen data durability—that is to reduce the audio files’ susceptibility to loss, accidental deletion, corruption, or system outages—the encrypted audio files (including full backups of files) are stored redundantly across multiple locations in secured data centers and other databases across the United States.
With traditional sharing methods, files can go missing or fall into the wrong hands when distributed physically via DVDs, CDs, or USB drives. Instead, through the Cloud Platform, courts can provide controlled access to recordings and transcripts, which can be tracked, updated, or revoked—unlike mailing a CD to someone. Additionally, sealing and unsealing features for court recordings contribute to this controlled access.
Knowing who played or streamed a court recording is a crucial element for fraud detection. Activity logs highlight the details of access to recordings by identifying who played a recording, where they were, and which device they used. Activity logs can even pinpoint the exact part of the recording that was played.
Audit logging shows all events in the system, including log ins, permissions changes, file uploads, etc. These features allow courts to audit access and changes to the system, meaning any unauthorized activity will be immediately visible. To control the distribution, courts can select exactly the audio they want down to the second—however long or short they like.
For The Record works with our clients to assist them in their risk assessments and compliance efforts. As agencies interpret their compliance requirements, we will collaborate to find a suitable approach that is consistent with relevant standards, including the Criminal Justice Information Services (CJIS) Security Policy.
This defines a minimum set of requirements for security controls around CJIS data, with the aim of protecting CJIS data whether at rest or in transit. The policy covers controls around the creation, viewing, modification, distribution, storage and destruction of CJIS data.
There is a shared responsibility with our clients for information security. For The Record and its cloud provider partners maintain and protect the server-side environment of FTR Justice Cloud. Within the cloud platform, we give our clients tools to assist in the management and security of their tenancy and usage. Clients are responsible for managing their client-side environment, keeping courts in control of their data.
With FTR Justice Cloud, the client’s responsibilities include:
FTR Justice Cloud employs numerous measures that combine to secure against hackers and prevent anyone other than authorized users from entering the restricted platform. Our solutions are designed to guard the sensitive and often protected information collected and stored within the justice system.
That’s why our security team, software, and cloud-based solutions:
In the unlikely scenario that a breach of the platform occurs, our platform has additional layers of defense to prevent the digital record being reached, opened, or compromised.
These include:
Although no technical provider or company can guarantee an online system is impossible to penetrate, shoring it up with multi-layered protections––protections that make it very difficult to break into––is the best defense available.
An argument that is often presented against the use of digital recordings is that digital files can be manipulated, potentially corrupting the verbatim record. Unfortunately, deep fake videos and voice cloning examples have shown us how realistic such counterfeits can be. But it is essential that, if a court record is challenged, the accuracy of the digital file can be verified.
With For The Record’s Cloud Platform, the authenticity of a file is secured by technologies such as the use of digital checksums and For The Record’s astute approach to file sharing.
Digital checksums are best described as a data file’s fingerprint, whereby even a small change to the file will cause the checksum to change completely. Checksums are safely stored so they can be compared with file copies to detect if unwanted changes have occurred. This is a reliable way to detect fraud, so altered files, deep fakes, or cloned audio can be identified.
This is the world’s best-practice technology and will provide the definitive answer if the content of a record is challenged.
There is no single measure that will, alone, protect a digital file from attack and provide courts with the confidence they need to be cybersafe.
But when industry best-practice processes are combined with For The Record’s technology innovations and data defenses, any attempt to infiltrate a file need not end up a judicial disaster. With forward planning and technical innovations, the court record can be protected, while maintaining transparency, accessibility, and efficiency.